Those who abuse AD CS almost immediately regret it, as the attack paths—often referred to by shorthand names of numbered escalation variants (ESC1, ESC4, and so on)—can lead to instant domain compromise under certain conditions. Unfortunately, this happens very frequently.
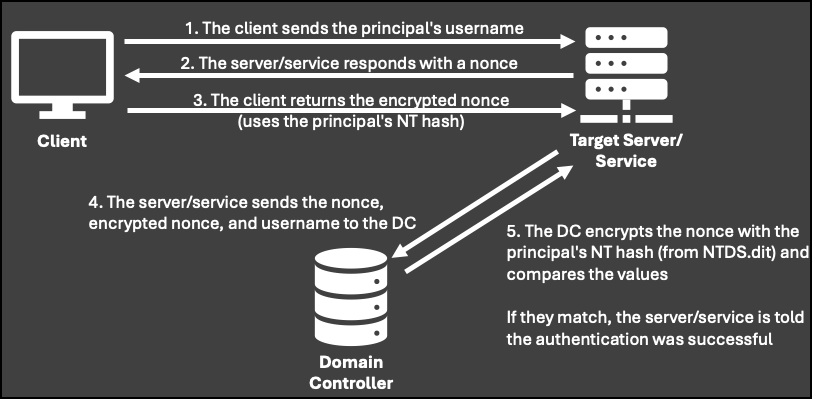
As the name implies, AD CS manages the issuance of cryptographic certificates and public key infrastructure (PKI) within an Active Directory environment. When combined with Public Key Cryptography for Initial Authentication (PKINIT), these certificates can be used with Kerberos to authenticate as a principal user without a password.
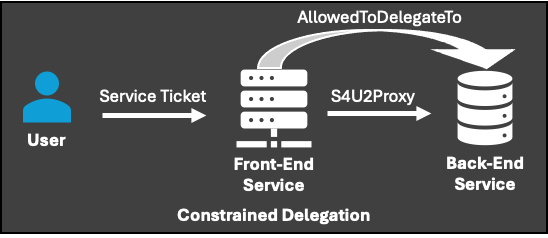
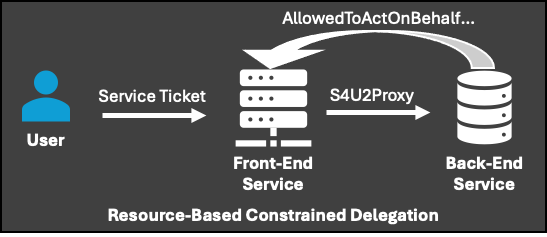
Even if PKINIT is not enabled in the environment, certificates can still often be used to authenticate to other protocols, such as Lightweight Directory Access Protocol (LDAP) over TLS. This can lead to secondary attacks, including the configuration of Resource-Based Constrained Delegation.
Of all the escalation paths CrowdStrike has observed in its operations, ESC1, ESC4, and ESC8 are the most commonly abused by adversaries.
ESC1
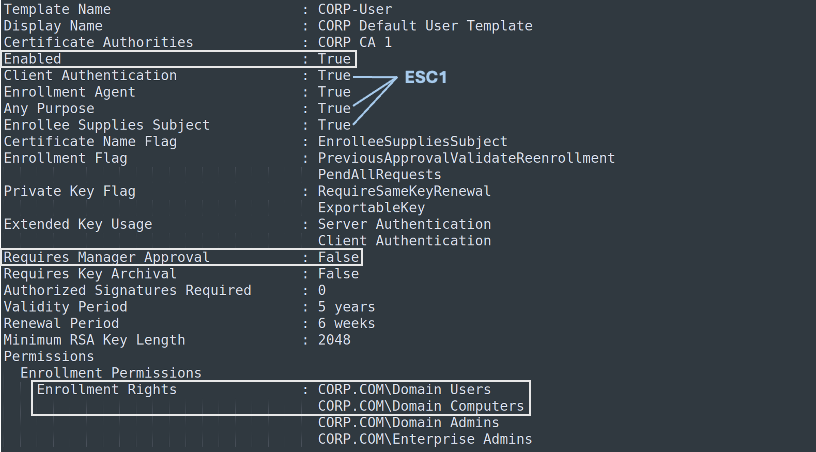
This attack path involves configurations that allow an attacker to request a certificate with a specified additional identifier, enabling them to impersonate a target account. The vulnerable combination of settings for this attack path includes:
- Large built-in groups (typically Domain Users, Domain Computers, or Authenticated Users) are allowed to enroll using the template and certification authority.
- Manager approval is disabled, although this is not a decisive factor if some social engineering or luck is involved (for example, inattentive managers).
- The target certificate template is enabled.
- Extended Key Usage (EKU) is set to a value that allows some form of Kerberos authentication (for example, Client Authentication), EKU is set to “Any Purpose,” or no EKU is specified at all.
- The certificate template is marked with ENROLLEE_SUPPLIES_SUBJECT, allowing the requester to specify an additional subject attribute when requesting a certificate.
When these conditions are met, a user can specify the name of a domain administrator or a domain controller and obtain full Kerberos authentication without knowing the password.
When using the open-source Certipy tool to enumerate AD CS, the template shown below would be vulnerable to ESC1.
It is worth noting that even if a certificate cannot be requested by these large built-in groups, it may still provide a path—albeit a slightly longer one—to domain privilege escalation. This occurs when non–Tier 0 principals are able to enroll in a vulnerable template. For example, it is often observed that individual servers have enrollment permissions on vulnerable templates, which adversaries later abuse to compromise the domain after obtaining local administrator privileges on those servers.
Mitigation: To protect against ESC1, ensure that certificate templates do not include the ENROLLEE_SUPPLIES_SUBJECT flag. If other deployed technologies absolutely require subjects to supply an alternative subject name, ensure that enrollment permissions are restricted and denied to high-privilege groups such as Domain Admins and Domain Controllers. If this is also not feasible, consider requiring manager approval for certificate requests to help identify illegitimate use.
It is also advisable to review templates where “Any Purpose” is specified or where no EKU is defined at all. In general, “Any Purpose” and missing EKUs should be adjusted to support only the limited set of usages required for that certificate.
ESC4
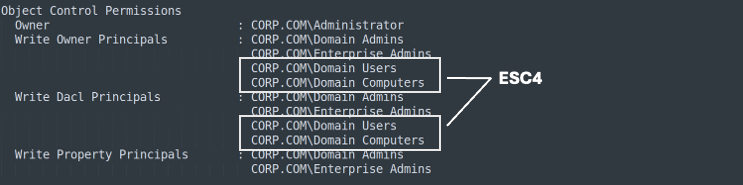
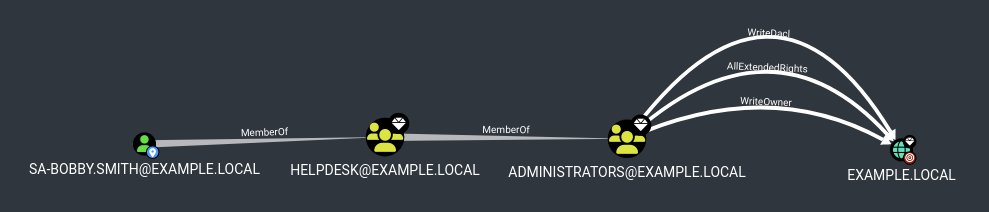
Certificate templates are Active Directory objects, like everything else in that environment, and ESC4 abuses misconfigured access control entries (ACEs) on those templates. With the ability to modify a template, an adversary can intentionally make it vulnerable by applying the settings described above for ESC1.
When enumerated again using Certipy, the template shown below would be vulnerable to ESC4.
Mitigation: ESC4 follows a more traditional approach. Because template owners/authors can escalate to Domain Admin by modifying a template, permissions on template objects must be reviewed, and ownership and other write permissions should be restricted to Domain Admins wherever possible. Tools such as Certipy can help identify these owners, as can traditional Active Directory reconnaissance tools like BloodHound.
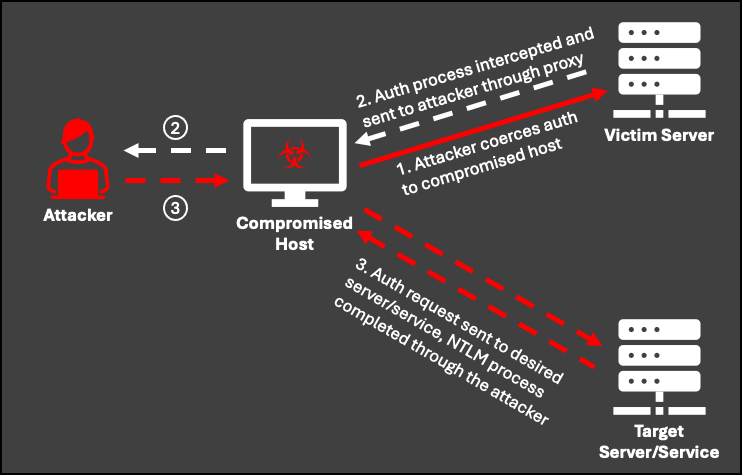
ESC8
Rather than abusing a template, ESC8 abuses the web enrollment capability on the certification authorities themselves. The CA web enrollment service allows users to perform certificate-related tasks through the CA web user interface by accessing the endpoint http(s)://ca-name.example.com/certsrv.
While this functionality can be useful for non-technical users, it can also be abused via NTLM relay attacks.
SMB and LDAP signing are defensive options that can prevent NTLM relay attacks against those respective services, but ESC8 targets the HTTP service, which is not protected by these controls.
After successfully completing authentication through an adversary-in-the-middle, the attacker can use the resulting session with tools such as Certipy or ntlmrelayx. This is done to automatically request a certificate for any template the victim is allowed to use and can lead to outcomes such as authenticating as the victim account or abusing other vulnerable templates that are not broadly accessible. If the victim is a domain controller, full domain compromise typically follows shortly thereafter.
Mitigation: For ESC8, consider fully removing the web enrollment service. If the service is still required, Microsoft has provided additional protection through Extended Protection for Authentication (EPA). It is also necessary to require HTTPS for access to the web enrollment endpoint to enforce a TLS tunnel, and to further restrict credential relay, NTLM authentication should be disabled for Internet Information Services (IIS) on the certification authority. For additional details on these defensive measures, refer to Microsoft documentation.